In the following, we show concrete practical examples of how attackers can create and send fake emails - and why the correct configuration of email security measures such as SPF or DMARC is essential.
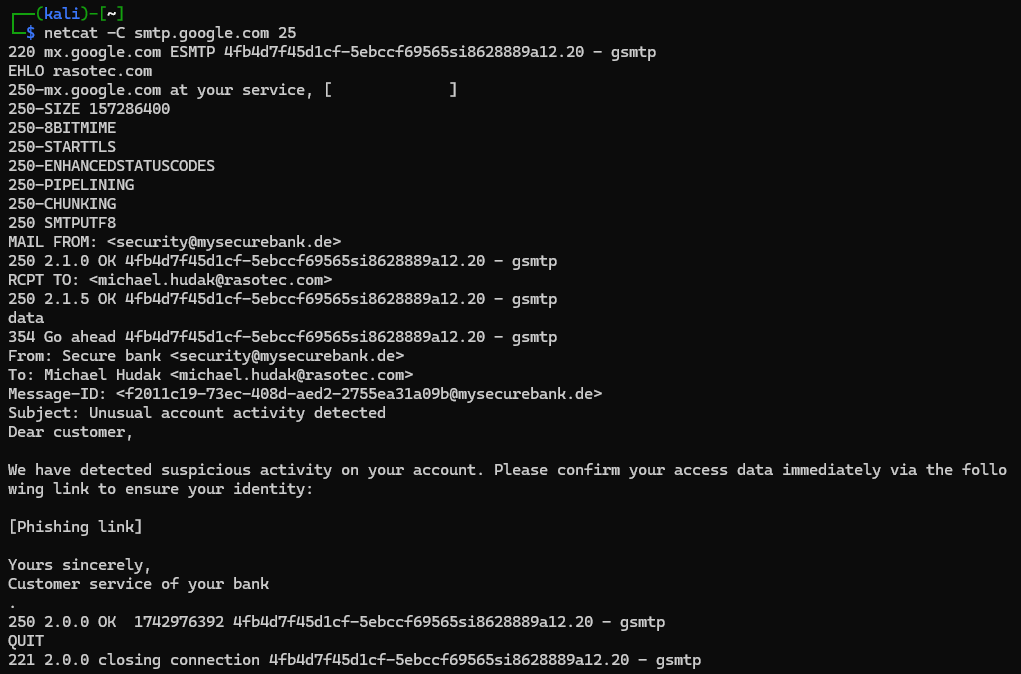
Spoofing from outside without SPF
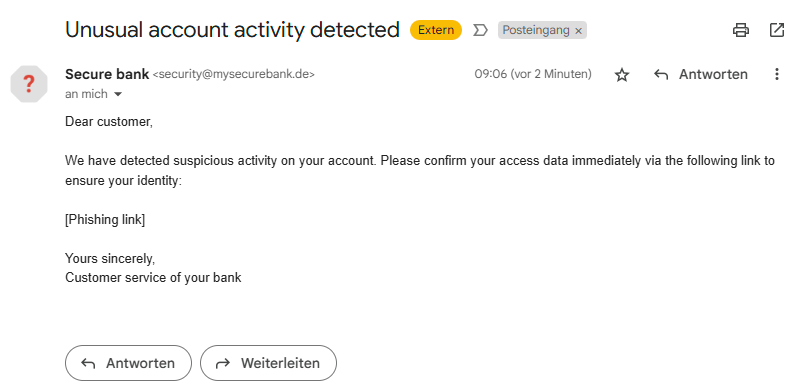
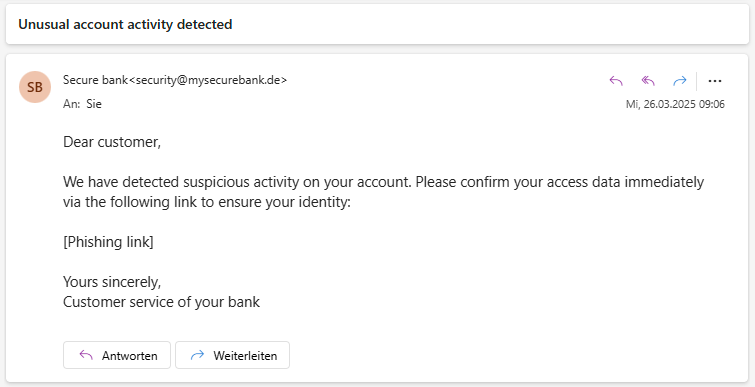
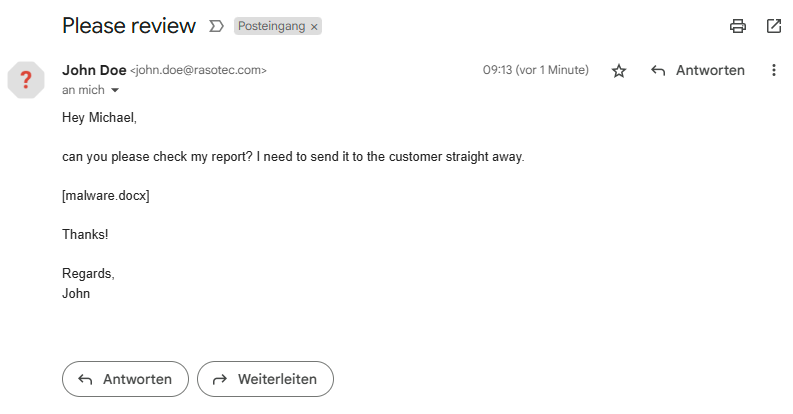
Imagine you receive an e-mail that appears to come from your bank:
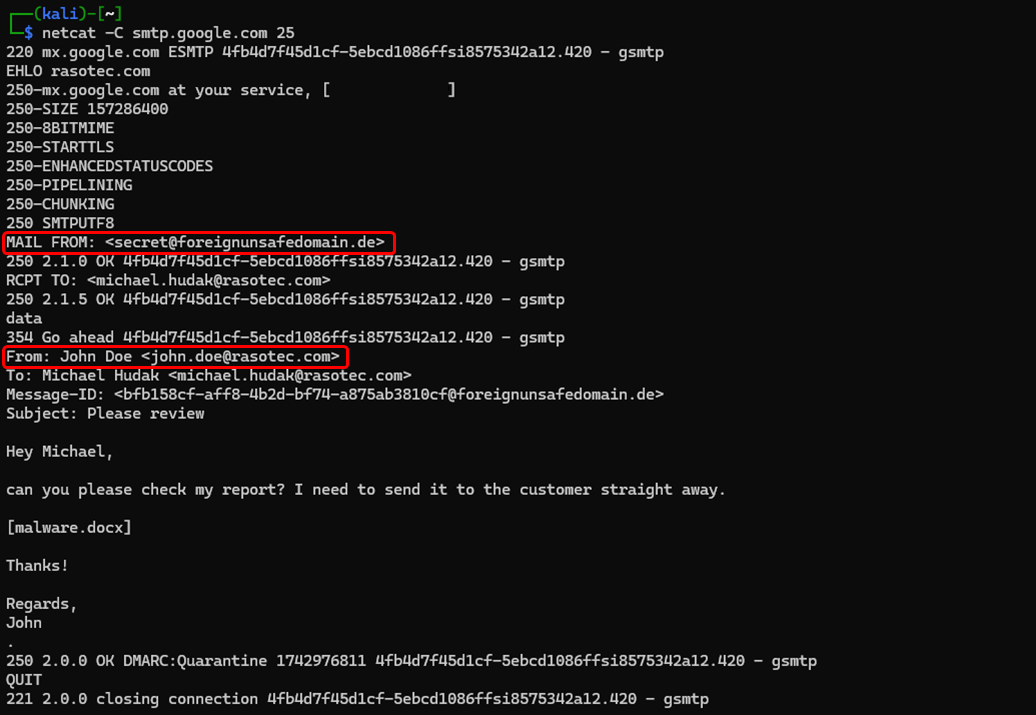
The image on the left shows the email in Gmail, the image on the right in Outlook. At first glance, this message looks legitimate and appears to come from your bank. However, a fake email like this can be created quickly and easily. The following screenshot shows exactly how this email was sent:
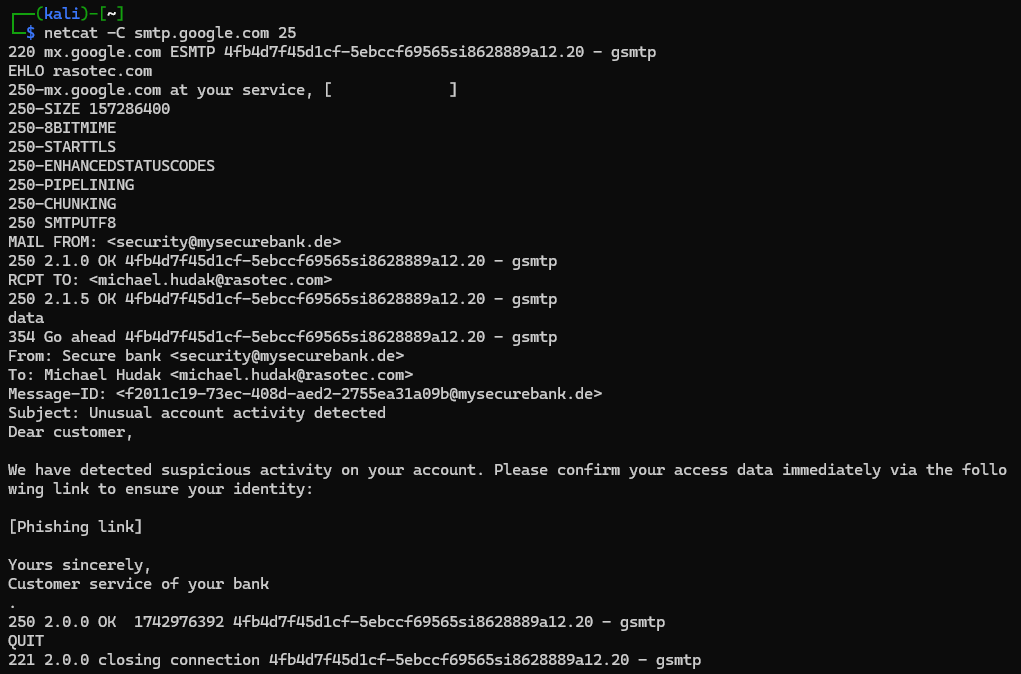
Communication takes place via TCP with the Linux tool netcat, whereby each message is one line. The server responds with a three-digit number at the beginning of the line and the remaining lines are user input. All entries can be chosen at will, for example the address after "MAIL FROM" and "From". Attackers do not need any login details or special information - authentication is not required.
The highlight of this method is that in many cases the recipient cannot recognize that the email is fake. If the sender's server has not configured an SPF (Sender Policy Framework), the recipient's email provider cannot check and authenticate the sender. This increases the risk of falling victim to a phishing attack. Conversely, attackers can also send emails in your name if your SPF configuration is incorrect or does not exist at all.
Note: In the example above, the domain is not registered. However, this does not matter and the attack also works with a registered domain. Only the SPF entry is decisive for the authorization to send an e-mail from this domain.
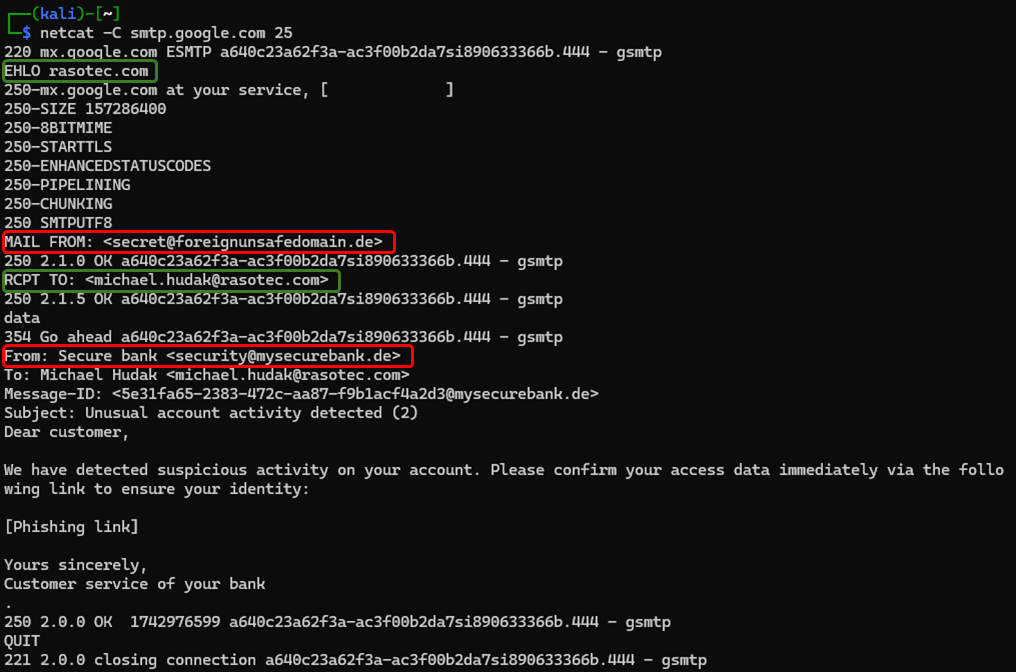
Spoofing from outside without DMARC
You may have noticed that the sender address appears several times in the communication with the e-mail server: once as part of the SMTP protocol (Envelope From) and once in the actual e-mail header (From). This can be exploited, for example, if you specify two different sender addresses:
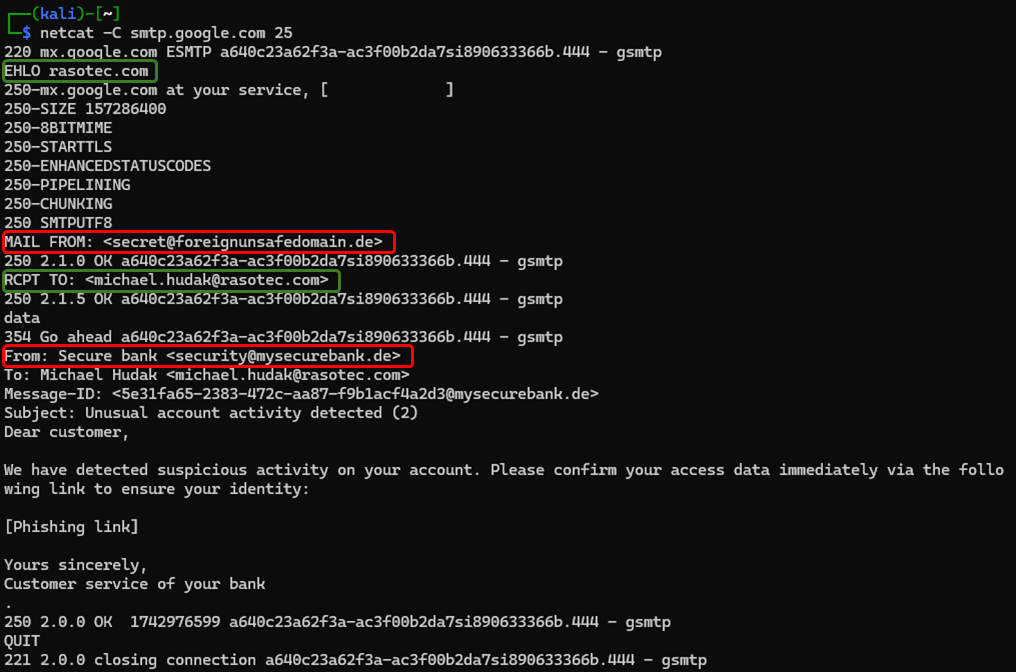
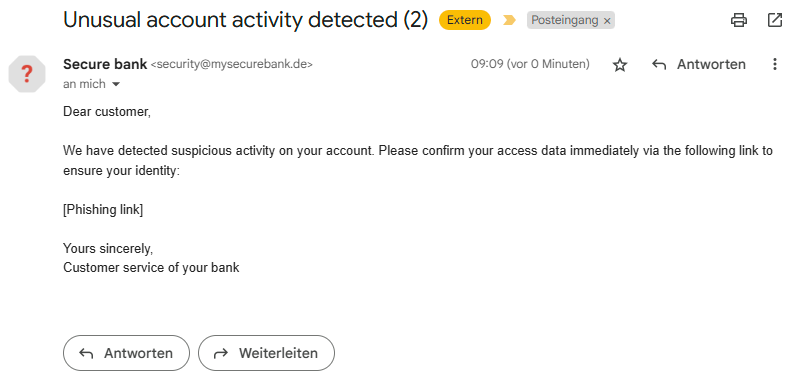
The e-mail server now checks the address after "MAIL FROM" for SPF. However, the address from the "From" header is displayed in the inbox:
Although the technical sender address has changed, there is no visible difference for the recipient in the inbox. This shows how easy it is to manipulate sender details. An attacker can exploit this by using a domain that has correctly implemented SPF as the first sender address (mail from). In this case, the email server receives an email from an SPF authenticated sender. This is also relatively simple, as the attacker can use any domain.
And this is where DMARC (Domain-based Message Authentication, Reporting and Conformance), specifically DMARC alignment, comes into play: If DMARC is set up correctly, the recipient's email provider will in many cases recognize the discrepancy between the Mail From address and the From address. Without DMARC, however, this protection does not apply.
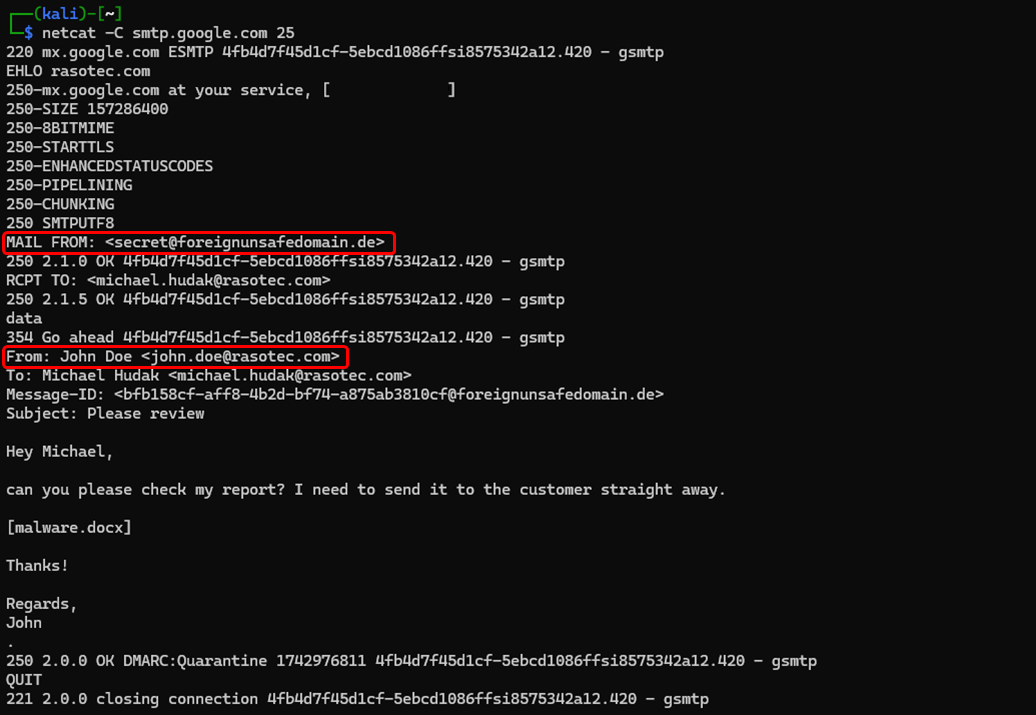
Spoofing to internal
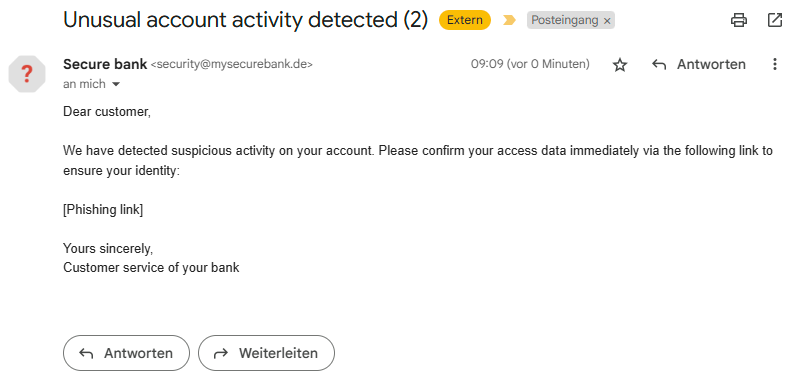
The next question is: What happens if an internal colleague appears as the forged sender address? Let's look at another example in which we create a new email:
In the inbox, it now appears as if the email came from a colleague with the same email domain:
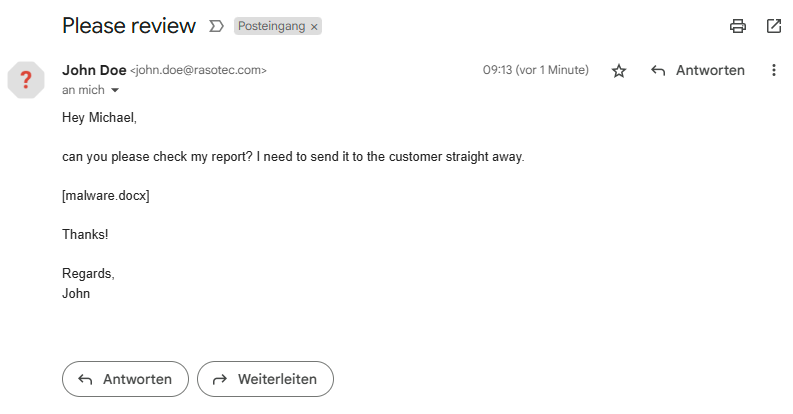
At first glance, this message is no different from a genuine internal email. This allows an attacker to exploit trust, as many employees are more likely to respond to emails from internal addresses or open links and attachments.
This attack should also be recognized by most mail servers if SPF and DMARC are configured correctly. However, we often come across vulnerable servers in our pentests. The email server should therefore also be configured so that no internal sender addresses are accepted from outside. Both Microsoft and Google offer corresponding options in their admin settings to better secure internal communication.
Summary
These examples show how easy it can be to manipulate sender addresses and send deceptively genuine phishing emails. With correctly set up security mechanisms such as SPF, DMARC and DKIM as well as suitable settings on your own email server, many of these attacks can be intercepted at an early stage and also operate independently of any SPAM analyses. Regularly checking and updating these configurations is therefore essential to effectively protect your company or organization from spoofing attacks.